That stack of sensitive documents sitting on your desk won’t shred itself. You’ve probably fed papers into a shredder countless times, but have you ever wondered what happens inside that humming machine that turns confidential reports into unreadable confetti? Understanding how does a paper shredder work is crucial for selecting the right model, preventing frustrating jams, and ensuring your sensitive information stays truly secure. Whether you’re protecting financial records, personal identification, or business secrets, knowing the mechanics behind document destruction helps you make informed decisions about your security needs.
Most people treat their paper shredder like a black box—feed in documents, press a button, and out come tiny paper particles. But the reality involves precise engineering that transforms potentially compromising information into completely unreconstructable pieces in seconds. From the moment paper touches the feed opening to its final resting place in the waste bin, a series of coordinated mechanical processes work together to guarantee security. This knowledge isn’t just interesting—it’s practical. When you understand how does a paper shredder work, you’ll avoid common mistakes like overloading or using the wrong cut style for sensitive materials.
Why Your Shredder’s Cutting Mechanism Determines Security Level
The heart of every paper shredder contains interlocking metal components that physically destroy documents, but not all cutting systems provide equal protection. When you feed paper into your shredder, two precisely engineered cylinders immediately begin the destruction process. These aren’t simple blades—they’re hardened steel gears with precisely angled teeth designed to slice paper with surgical precision. As the cylinders rotate in opposite directions, their interlocking teeth create a powerful shearing action that pulls paper inward while simultaneously cutting it into predetermined shapes and sizes.
The specific arrangement of these cutting teeth determines your security outcome. In higher-security models, the blades follow complex patterns that create tiny diamond or particle shapes rather than simple strips. This engineering detail is why understanding how does a paper shredder work matters—you might think all shredders offer equal protection, but the cutting mechanism design directly impacts whether someone could potentially reconstruct your shredded documents. When shopping for a new shredder, examine the cutting mechanism specifications rather than just power ratings, as this component ultimately determines your document security level.
What You Should Look For in Cutting Cylinder Quality
High-quality shredders use hardened steel cylinders that maintain their sharpness through thousands of sheets. Cheaper models often use lower-grade metals that dull quickly, causing incomplete shredding and frequent jams. When purchasing a shredder, check if the manufacturer specifies the steel grade—look for terms like “hardened steel” or “industrial-grade steel.” The spacing between cutting teeth also matters significantly; tighter spacing creates smaller particles but requires more motor power. For home use handling occasional sensitive documents, cross-cut cylinders with 5/32-inch particle size provide excellent security. Businesses dealing with highly confidential information should seek micro-cut mechanisms producing particles smaller than 1/8 inch.
How Paper Actually Gets Pulled Into and Through Your Shredder
That moment when you feed paper into your shredder and it suddenly grabs and pulls the document inside isn’t magic—it’s carefully engineered feeding mechanics. Modern shredders use a combination of sensors and rollers to initiate the shredding process the moment paper contacts the feed opening. When you place a document against the safety flap, optical sensors detect its presence and activate the motor, which engages the feed rollers. These rollers, made of high-friction rubber or plastic, grip the paper firmly and pull it toward the cutting cylinders with surprising force.
Why Your Shredder Suddenly Stops Mid-Operation
Ever fed paper into your shredder only to have it stop after a few inches? This frustrating experience usually stems from the overload protection system kicking in. When paper resists the cutting action—perhaps because you’ve exceeded the sheet capacity or encountered a particularly thick document—the motor experiences increased resistance. Smart shredders detect this resistance spike and immediately reverse direction to prevent motor burnout. This safety feature explains why understanding how does a paper shredder work helps prevent damage: never force paper through, and always respect the maximum sheet capacity listed in your manual. If your shredder reverses frequently, reduce the number of sheets per pass rather than assuming it’s broken.
What Causes Those Annoying Paper Jams and How to Prevent Them
Paper jams typically occur when foreign materials interfere with the cutting mechanism or when paper fibers bind between the cylinders. Staples, paper clips, and even certain types of glossy paper can cause immediate jams in most shredders. The solution? Always remove metal fasteners before shredding, and check your shredder’s specifications for compatible paper types. For frequent jam prevention, regularly oil the cutting cylinders using shredder-specific lubricant—never use household oil, which can gum up the mechanism. Most quality shredders include a reverse function specifically for clearing minor jams; use this feature at the first sign of resistance rather than continuing to feed paper.
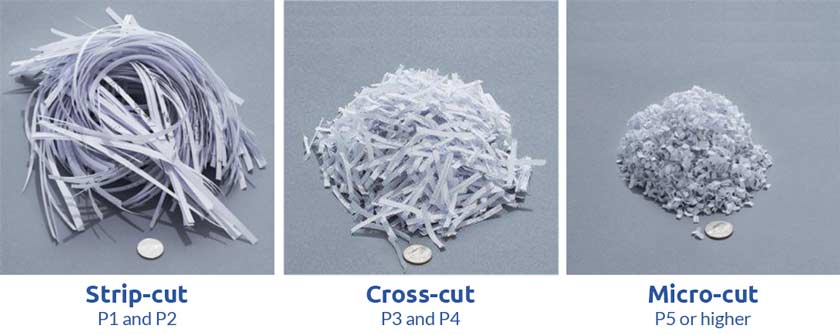
Strip-Cut vs. Cross-Cut vs. Micro-Cut: Which Shredder Actually Protects Your Data?
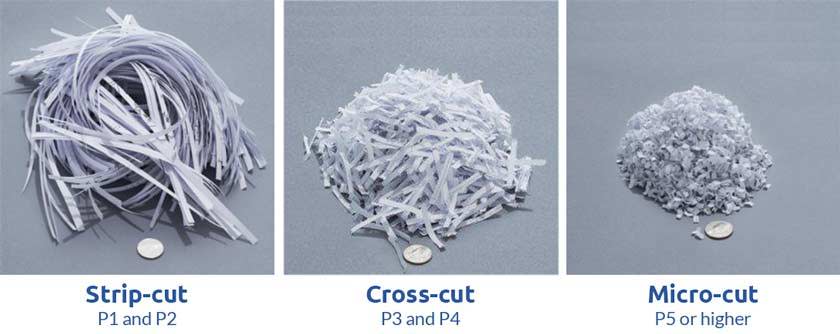
The difference between basic strip-cut shredders and high-security micro-cut models represents a massive security gap you shouldn’t ignore. Strip-cut shredders, the most basic and affordable type, slice paper into long, narrow strips running the length of the document. While this destroys the document’s immediate readability, reconstruction is surprisingly possible—like solving a jigsaw puzzle with only a few dozen pieces. Identity thieves have successfully reconstructed financial documents from strip-cut shreds, making this method inadequate for truly sensitive information.
Why Cross-Cut Shredding Provides Serious Document Security
When you need reliable protection for tax records, medical documents, or business contracts, cross-cut shredders deliver substantially better security through their crisscross cutting pattern. These machines use two sets of interlocking blades that slice paper both lengthwise and widthwise, creating small diamond or rectangle-shaped particles. The resulting confetti-like output contains hundreds of pieces per document sheet, making reconstruction practically impossible without industrial-level resources. For most home offices and small businesses handling sensitive but not classified information, cross-cut shredders provide the ideal balance of security, speed, and affordability. Look for models rated P-4 or higher on the DIN 66399 security scale for adequate protection against determined reconstruction attempts.
When You Absolutely Must Choose a Micro-Cut Shredder
For government agencies, healthcare providers, or financial institutions handling highly classified information, only micro-cut shredders provide sufficient security. These industrial-grade machines dice paper into thousands of tiny particles smaller than a fingernail clipping. The cutting mechanism involves multiple stages of precision blades working in sequence to reduce paper to near-pulverized state. While micro-cut shredders process documents more slowly and cost significantly more, they’re the only consumer-available option meeting top-tier security standards (DIN 66399 level P-7). If you handle social security numbers, medical records, or financial data that could enable identity theft, investing in micro-cut technology isn’t just recommended—it’s often legally required by data protection regulations.
Critical Performance Factors That Determine Your Shredder’s Real-World Effectiveness

Your shredder’s sheet capacity rating isn’t just a suggestion—it’s a critical parameter for preventing damage and ensuring security. Exceeding the maximum sheet count causes immediate problems: the motor strains against too much resistance, cutting cylinders can’t fully penetrate all sheets, and partially shredded documents create security risks. Always follow the manufacturer’s sheet capacity guidelines, which are typically based on 20-pound paper at 80% humidity. If you regularly shred thicker paper like cardstock or multiple-page documents, reduce the sheet count by 25-50%. Smart shredder users develop the habit of feeding documents in smaller batches than the maximum rating, extending the machine’s lifespan while ensuring complete destruction.
How Run Time and Cool Down Periods Affect Daily Shredding Efficiency
That frustrating moment when your shredder suddenly shuts off mid-batch isn’t a defect—it’s an essential thermal protection feature. All shredder motors generate heat during operation, and continuous use beyond recommended run times causes dangerous temperature buildup. Most home-office shredders have 2-5 minute maximum run times followed by 20-30 minute cool-down periods. Commercial models handle longer continuous operation but still require periodic cooling. To maximize productivity, shred in cycles matching your machine’s duty cycle, and consider upgrading to a commercial-grade shredder if you regularly process large document volumes. Never bypass thermal protection systems—overheating permanently damages motors and creates fire hazards.
What Happens to Shreds After Destruction: Maximizing Security and Convenience
The journey of your documents doesn’t end when they enter the waste bin—proper shred management completes the security process. Most home shredders produce shreds that can be recycled with regular paper waste, but this creates a potential security vulnerability if someone retrieves the bin before disposal. For maximum security, mix shreds with food waste or other non-paper materials before disposal, or use a dedicated shred-only waste container with a locking lid. Commercial environments often employ locked shred containers with scheduled professional pickup services to maintain chain-of-custody for sensitive documents.
Smart Maintenance Habits That Extend Your Shredder’s Lifespan
Your shredder performs better and lasts longer when you follow simple maintenance routines informed by how does a paper shredder work. Monthly lubrication of cutting cylinders prevents paper fibers from binding between blades—a leading cause of jams and premature wear. Use only manufacturer-recommended shredder oil, applying it directly to the feed opening while the machine runs in reverse. Never use vegetable oil or WD-40, which attract dust and eventually gum up the mechanism. Additionally, empty the waste bin before it reaches 80% capacity to prevent overflow-related jams, and wipe the feed opening regularly to remove paper dust buildup. These small habits prevent 90% of common shredder problems while maintaining optimal security performance.
Understanding how does a paper shredder work transforms you from a passive user into an informed document security manager. By selecting the right cut style for your sensitivity needs, respecting operational limits, and performing simple maintenance, you ensure your shredder reliably protects your most confidential information. Remember that document security isn’t just about destruction—it’s about creating an unbroken chain from creation to final disposal. When you feed documents into your shredder, you’re not just operating a machine; you’re executing the final step in your information security protocol. Choose wisely, operate knowledgeably, and shred confidently knowing exactly how your documents become truly unreconstructable.